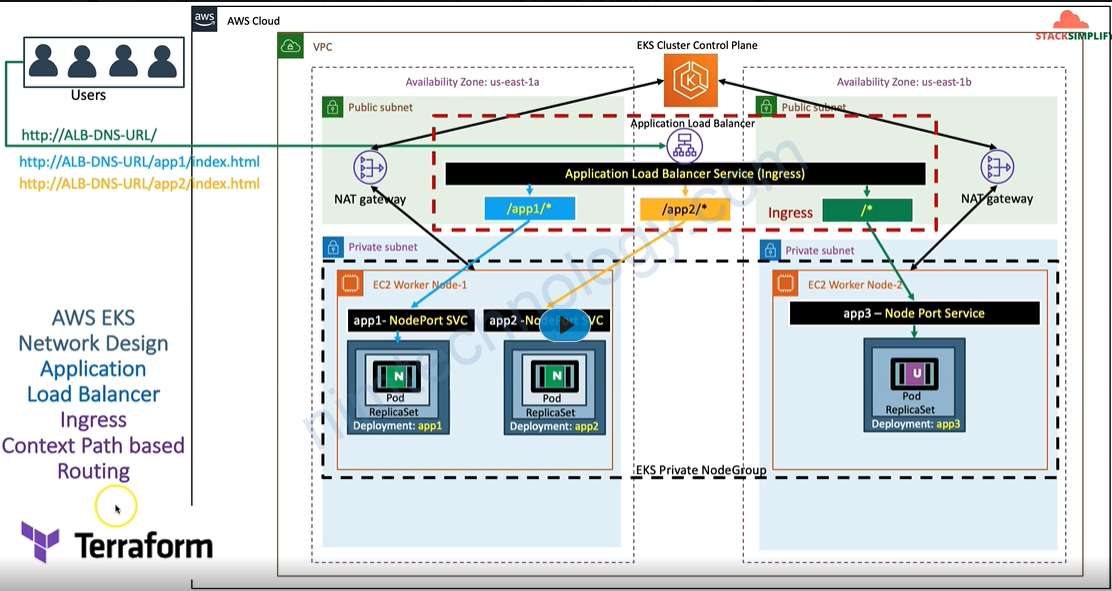
Mình có câu hỏi nếu công ty sài aws và chưa có vault thì trên AWS có feature take care được việc này hem nhỉ?

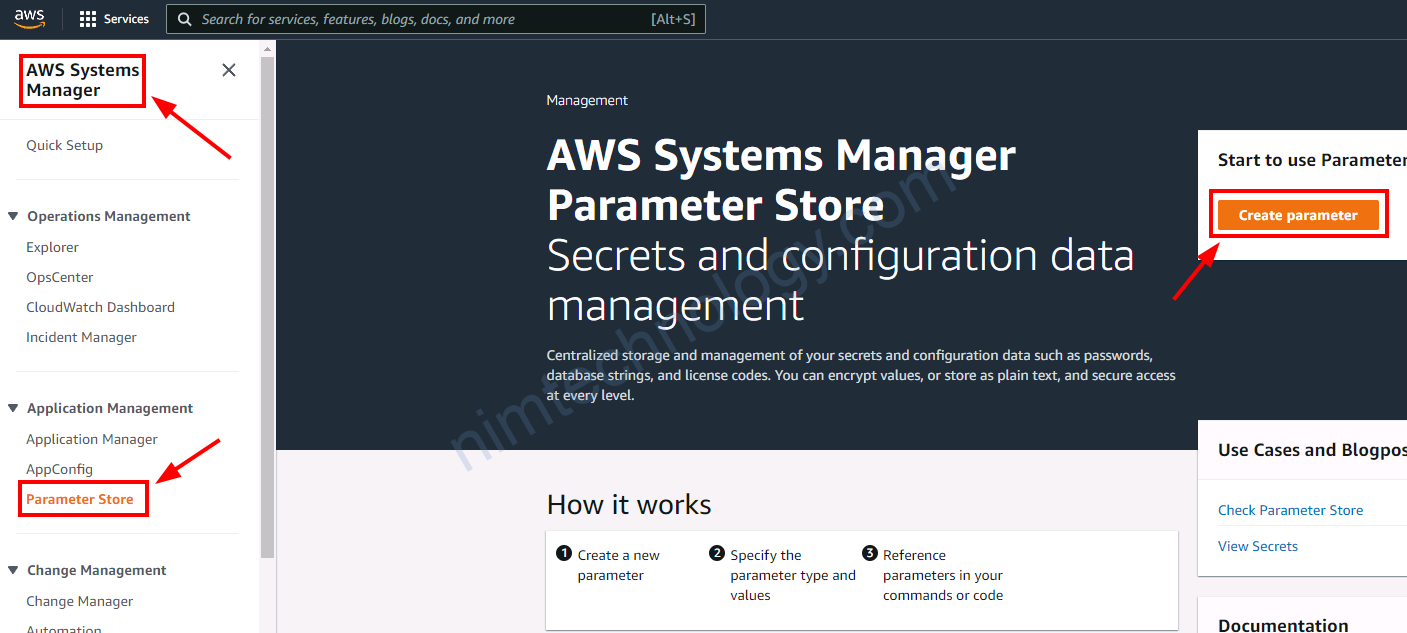
Ok nhà nghèo lab thì chơi SSM nhé
Manual by hand
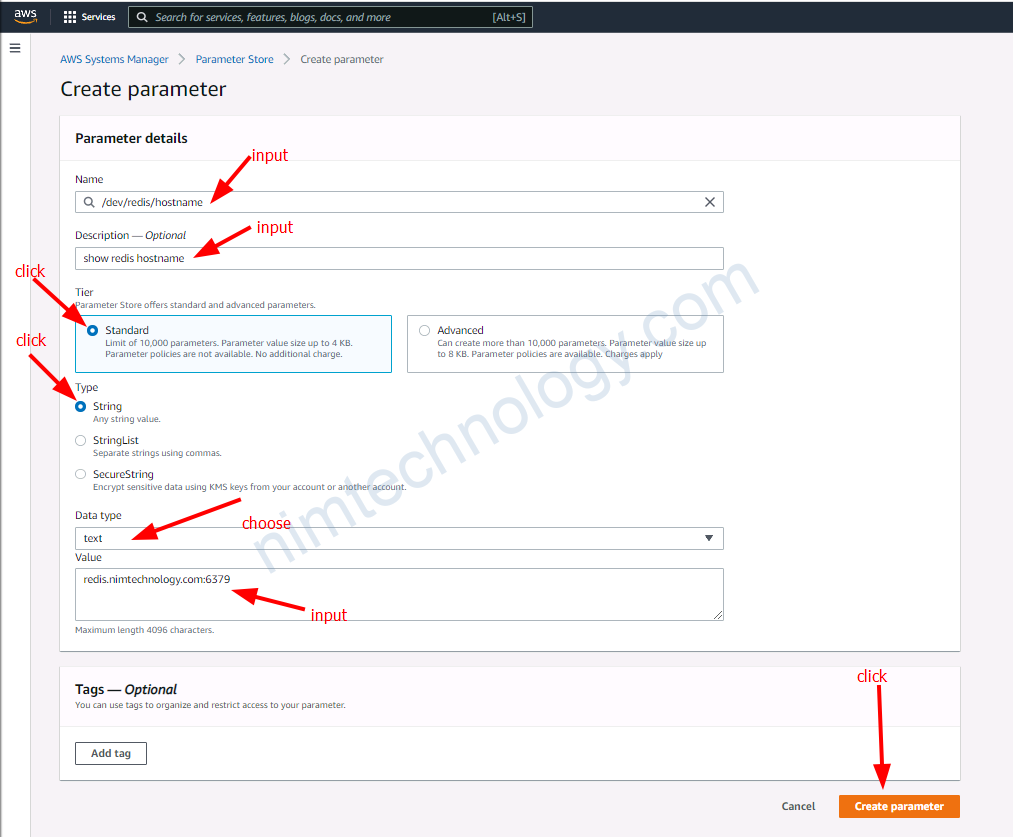
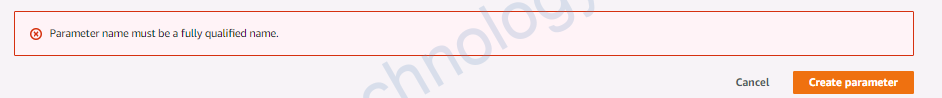
Khi mà mình tạo là dev/redis/hostname thì bị báo lỗi Parameter name must be a fully qualified name.
Giờ tạo bằng command
https://cloudaffaire.com/how-to-create-parameter-store-in-aws-ssm/
root@LP11-D7891:~# aws ssm put-parameter \
--region> --region us-east-1 \
ame "/d> --name "/dev/mysql/hostname" \
value "> --value "mysql.nimtechnology.com:3306" \
> --type String \
> --tags "Key=env,Value=dev"
{
"Version": 1,
"Tier": "Standard"
}
Nếu bạn có nhiều profile thì có thể thêm duôi sau: --profile tc-fedramp-dev-mdcl-nimtechnology-engines
Giờ thực hiện get mấy key này
root@LP11-D7891:~# aws ssm get-parameter --region us-east-1 --name "/dev/mysql/hostname" --query "Parameter.Value" --output text mysql.nimtechnology.com:3306 aaaaa bbbb root@LP11-D7891:~# aws ssm get-parameter --region us-east-1 --name "/dev/mysql/hostname" --query "Parameter.Value" --output text | xargs mysql.nimtechnology.com:3306 aaaaa bbbb
OK giờ mình sẽ tạo 1 user khác để và add policy cho user đó được quyền read secret Parameter Store
# Create IAM User
aws iam create-user --user-name readonly_ssm
# Create
aws iam create-policy \
--policy-name AmazonParameterStoreReadOnlyPolicy \
--policy-document \
'{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"ssm:GetParameter*"
],
"Resource": "arn:aws:ssm:us-east-2:123456789012:parameter/dev*"
}
]
}'
===>
==>output
{
"Policy": {
"PolicyName": "AmazonParameterStoreReadOnlyPolicy",
"PolicyId": "ANPATU2QSHIIT2RROSEYE",
"Arn": "arn:aws:iam::250887682577:policy/AmazonParameterStoreReadOnlyPolicy",
"Path": "/",
"DefaultVersionId": "v1",
"AttachmentCount": 0,
"PermissionsBoundaryUsageCount": 0,
"IsAttachable": true,
"CreateDate": "2022-08-31T06:39:57+00:00",
"UpdateDate": "2022-08-31T06:39:57+00:00"
}
}
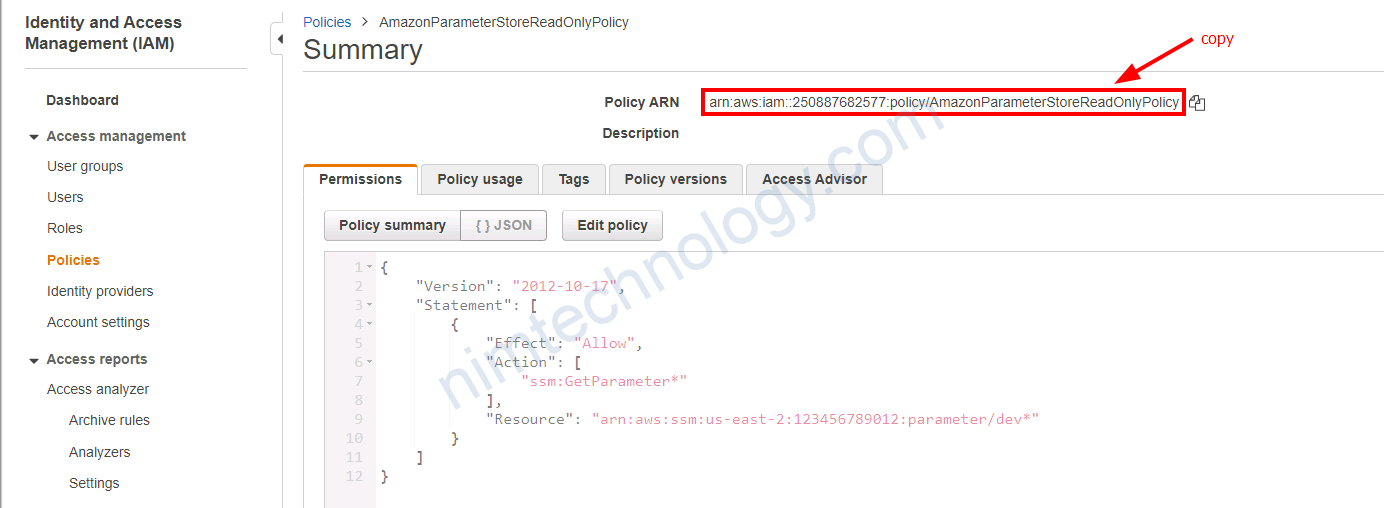
Mình đã create được policy theo ý mình, bạn nhờ copy Policy ARN
# Attach ParameterStoreReadOnly Policy to User
aws iam attach-user-policy --policy-arn arn:aws:iam::250XXXX577:policy/AmazonParameterStoreReadOnlyPolicy --user-name readonly_ssm
# Set password for readonly_ssm user
aws iam create-login-profile --user-name readonly_ssm --password @SSMXXXReadOnly --no-password-reset-required
#Credentials for IAM User and make a note of them
aws iam create-access-key --user-name readonly_ssm
# Make a note of Access Key ID and Secret Access Key
User: readonly_ssm
{
"AccessKey": {
"UserName": "readonly_ssm",
"AccessKeyId": "AKIATU2QSHIITN5ALD7E",
"Status": "Active",
"SecretAccessKey": "PGwAPd2VOZXXXXXXXXrAwY4GeiZLklBBTXMe+",
"CreateDate": "2022-08-31T06:47:24+00:00"
}
}
Giờ mình thực hiện thử get secret bằng user
Mình biết rằng mình đã sai cái Resource của IAM Policy
root@LP11-D7891:~# aws ssm get-parameter --region us-east-1 --name "/dev/redis/hostname" --query "Parameter.Value" --output text --profile default-readonly-ssm An error occurred (AccessDeniedException) when calling the GetParameter operation: User: arn:aws:iam::250887682577:user/readonly_ssm is not authorized to perform: ssm:GetParameter on resource: arn:aws:ssm:us-east-1:250887682577:parameter/dev/redis/hostname because no identity-based policy allows the ssm:GetParameter action
Để tìm được Resource ARN tạo đại rồi get thử là 1 cách
==> arn:aws:ssm:us-east-1:250887682577:parameter/dev/redis/hostname
Hoặc như trong bài viết bên dưới:
https://docs.aws.amazon.com/systems-manager/latest/userguide/security_iam_service-with-iam.htmlarn:aws:ssm:<region>:<account-id>:<maintenancewindow>/<window-id>
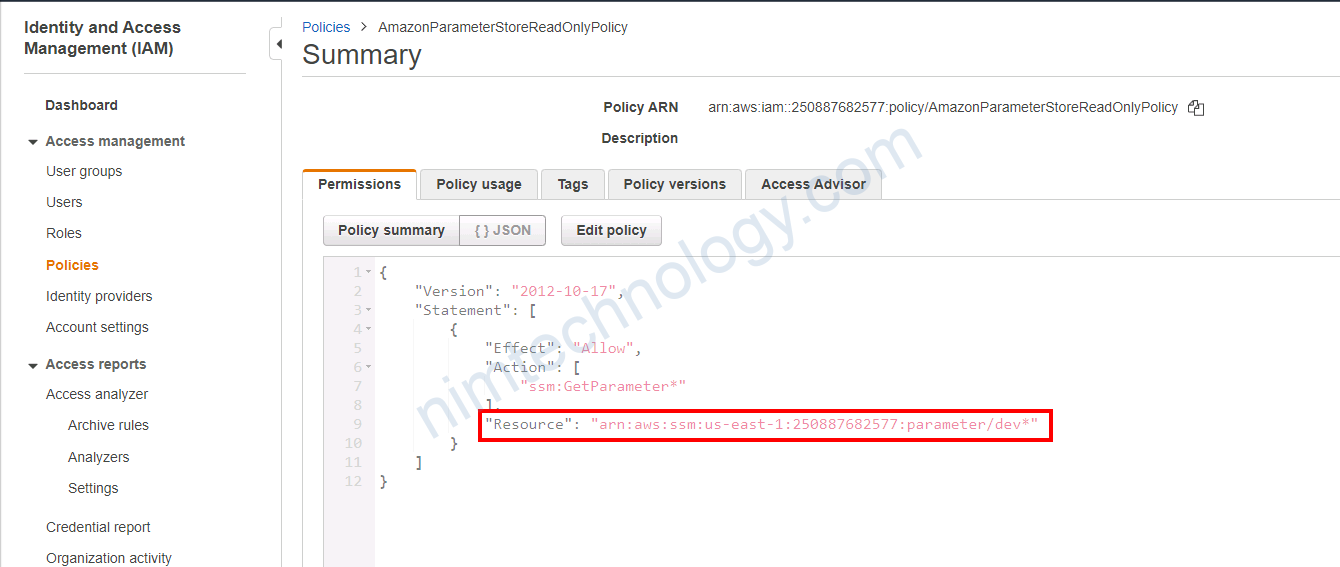
Ok giờ mình đã get được ok.
root@LP11-D7891:~# aws ssm get-parameter --region us-east-1 --name "/dev/redis/hostname" --query "Parameter.Value" --output text --profile default-readonly-ssm redis.nimtechnology.com:6379