Hello anh em!
Trước đó mình có hướng dẫn Install EKS cluster bằng terraform resource.
Bạn có thể tham khảo bài viết bên dưới.
Hôm nay chúng ta sẽ Install 1 cluster eks thông qua terraform module.
Mình sẽ sử dụng module này:
https://registry.terraform.io/modules/terraform-aws-modules/eks/aws/latest
Và đây là các bạn viết tham khảo:
(main) https://antonputra.com/amazon/create-eks-cluster-using-terraform-modules/
https://infraform.github.io/terraform-elastic-kubernetes/
https://github.com/alexlogy/terraform-eks-cluster
https://alexlogy.io/creating-eks-cluster-in-aws-with-terraform/
https://andrewtarry.com/posts/terraform-eks-alb-setup/
https://no-easy-dev.tistory.com/m/39
Upgrade from v17.x to v18.x
https://github.com/terraform-aws-modules/terraform-aws-eks/blob/master/docs/UPGRADE-18.0.md#upgrade-from-v17x-to-v18x
https://billhegazy.com/eks-terraform-module-upgrade-from-v17-to-v18/
Upgrade from v18.x to v19.x
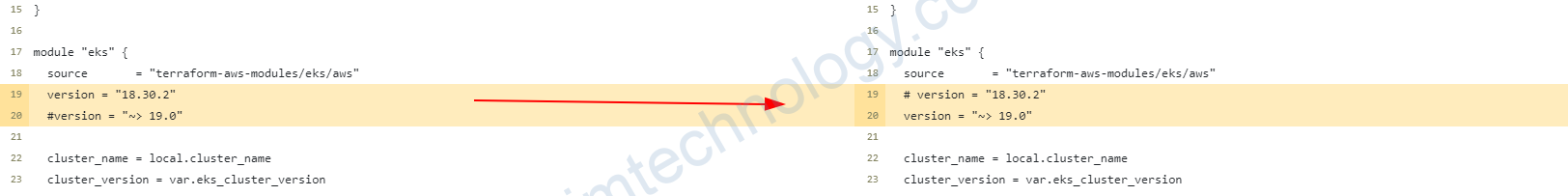
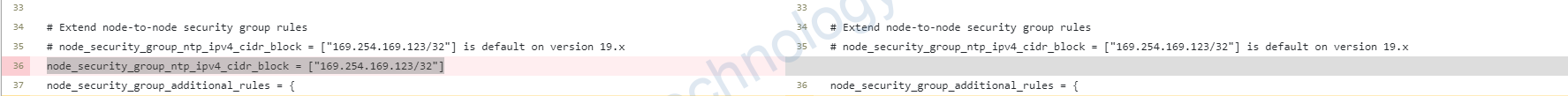
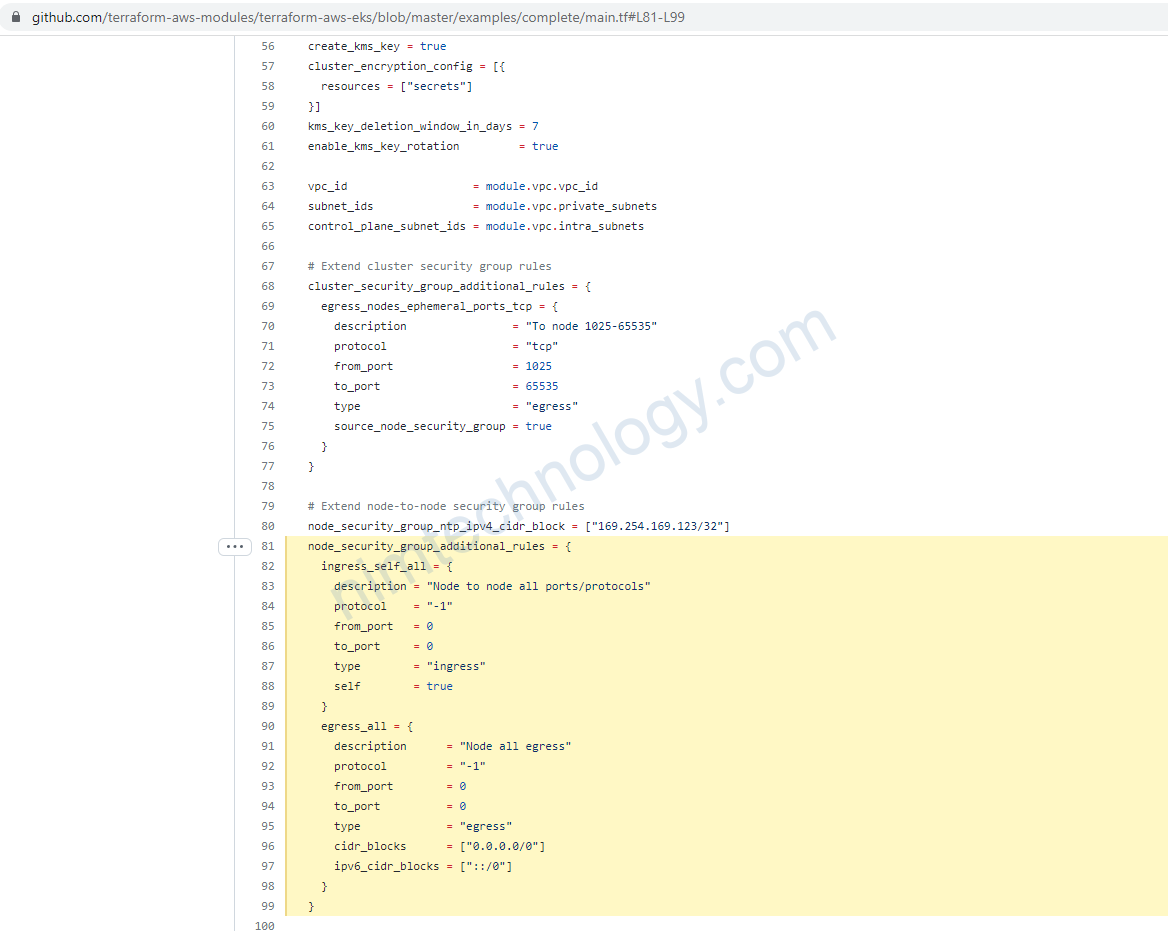
and delete all rules in node_security_group_additional_rules
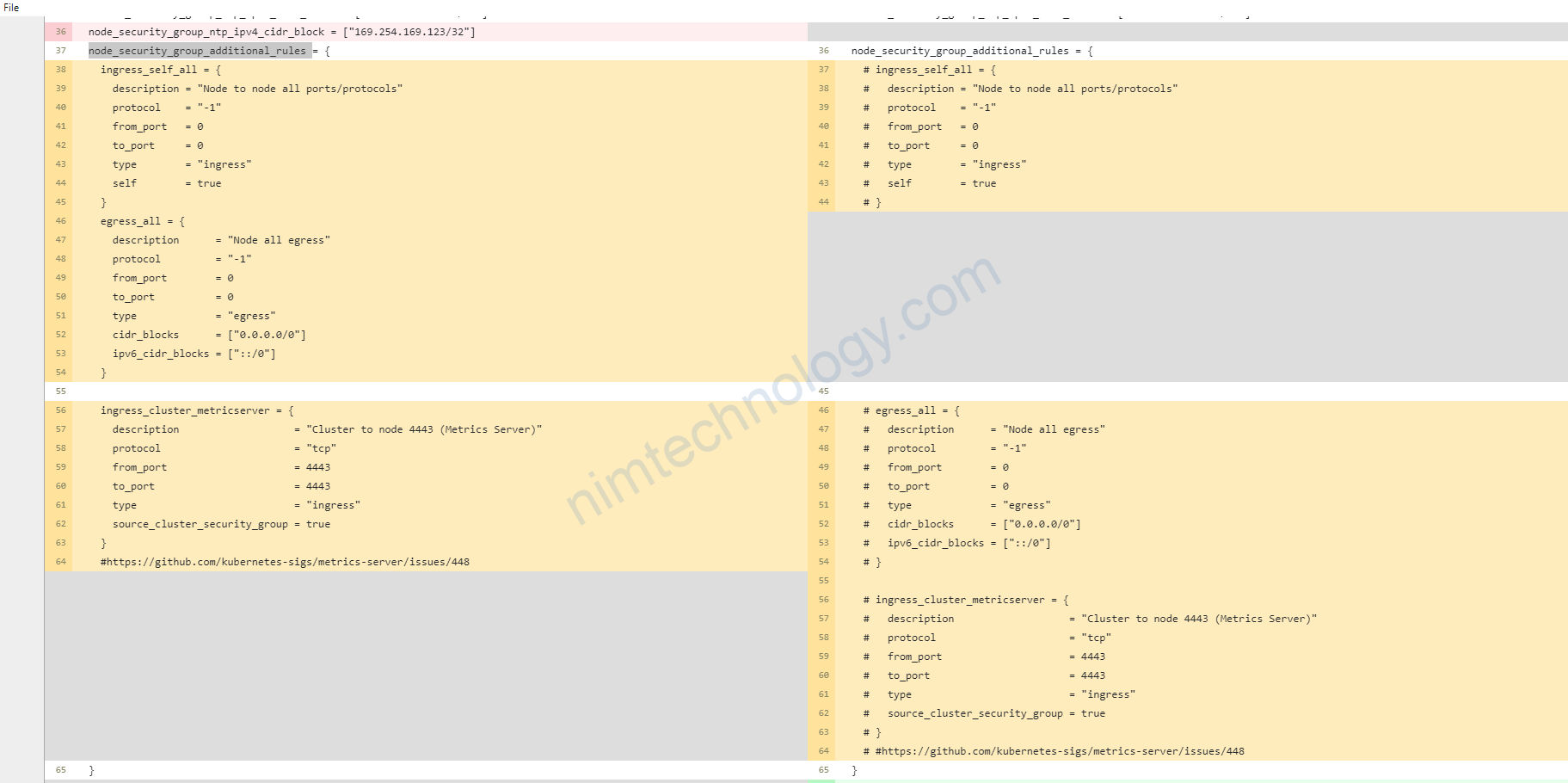
remove node_security_group_ntp_ipv4_cidr_block = ["169.254.169.123/32"]
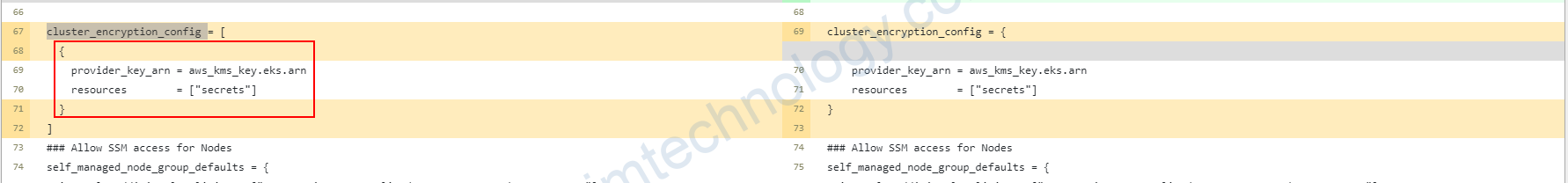
change cluster_encryption_config
Terraform EKS module version 19.x.x
Nếu bạn deploy mới thì có tham khảo code ở đây.
https://github.com/mrnim94/terraform-aws/tree/master/eks/eks_module/version-19.x.x/eks
1) Creating VPC to repair to EKS Cluster
Đầu tiên thì mình sẽ create VPC và bạn có thể tham khảo link dưới.
https://bitbucket.org/nimtechnology/aws-terraform/src/master/infra-structure/aws/250887682577/vpc/mdce-metadefender-devops/
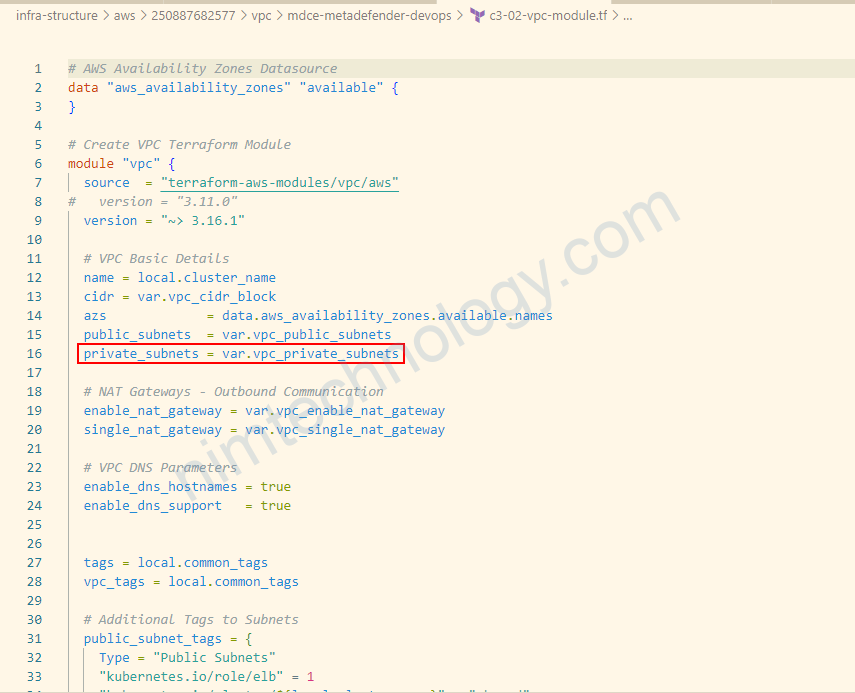
Ở phần VPC thì bạn cần lưu ý ở chỗ tag
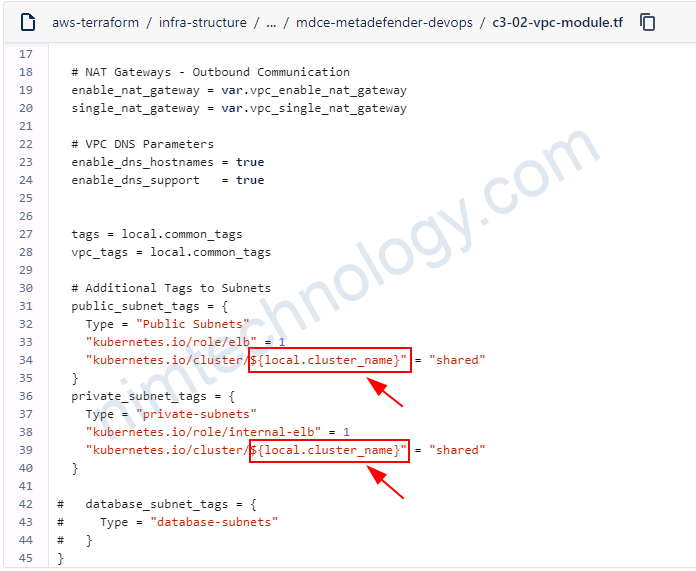
"kubernetes.io/role/elb" = 1
==> Tag này thì tạo svc LoadBalancer sẽ cập IP or Domain Public
"kubernetes.io/role/internal-elb" = 1
==> Tag này thì tạo svc LoadBalancer sẽ cập IP or Domain Private.
2) Create EKS cluster via terraform module(v18.x.x)
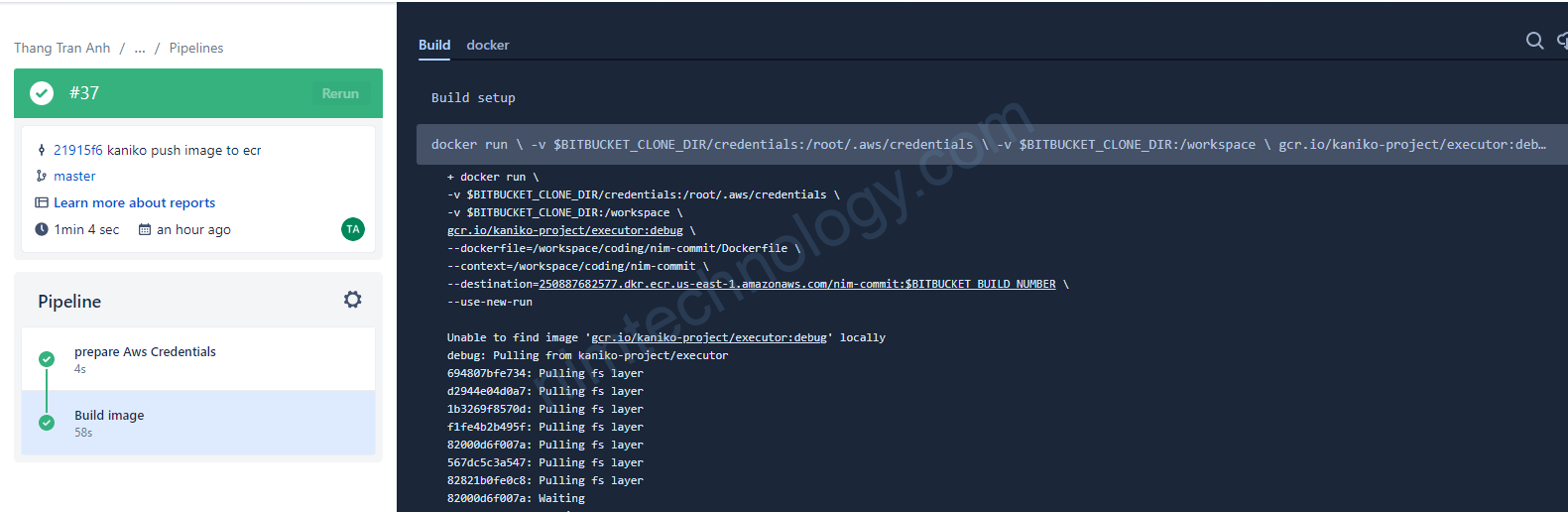
Hiện tai project này mình đang provisioning bằng bitbucket pipeline nên mình share qua bitbucket luôn.
Chúng ta sẽ đi vào từng khai báo
2.1) OpenID Connect Provider and IRSA

enable_irsa: Determines whether to create an OpenID Connect Provider for EKS to enable IRSA
nếu bạn vẫn thấy lạ với khai niệm trên thì có thể lab bài dưới.
2.2) Pods can’t connect the internet or need to be permited all outbound on eks
Sau khi bạn đã dựng eks cluster và bạn nhớ rằng mình chưa config terraform cho Security Group mục này cần thiết cho bạn
nếu pod của bạn không thể đi ra ngoài internet thì mục này cần thiết cho bạn
Cấu hình trong eks terraform module.
https://github.com/terraform-aws-modules/terraform-aws-eks/issues/1779#issuecomment-1203398170
2.3) Custom block storage for Node Group
Nếu bạn muốn chỉnh một số liên quan đến disk của worker EKS.
encrypt data, volume type,…
module "eks" {
source = "terraform-aws-modules/eks/aws"
version = "18.30.2"
....
....
eks_managed_node_groups = {
"general-${var.owners}" = {
# because HA ArgoCD, we need at least 3 nodes
desired_size = 3
min_size = 3
max_size = 10
block_device_mappings = {
xvda = {
device_name = "/dev/xvda"
ebs = {
volume_size = 100
volume_type = "gp3"
iops = 3000
throughput = 125
encrypted = true
delete_on_termination = true
}
}
}
labels = {
role = "general"
}
instance_types = ["t3.medium"]
capacity_type = "ON_DEMAND"
}
2.4) Update output
output "cluster_certificate_authority_data" {
description = "Base64 encoded certificate data required to communicate with the cluster"
value = module.eks.cluster_certificate_authority_data
}
output "cluster_endpoint" {
description = "Base64 encoded certificate data required to communicate with the cluster"
value = module.eks.cluster_endpoint
}
output "cluster_id" {
description = "Base64 encoded certificate data required to communicate with the cluster"
value = module.eks.cluster_id
}
output "oidc_provider_arn" {
description = "Base64 encoded certificate data required to communicate with the cluster"
value = module.eks.oidc_provider_arn
}
output "vpc_id" {
description = "The ID of the VPC is installed EKS Cluster"
value = data.terraform_remote_state.eks.outputs.vpc_id
}
Issues
does not automatically assign public IP addresses to instances launched into it
Error: waiting for EKS Node Group (devsecops-nim:general-devsecops-2023072807281029660000000e) to create: unexpected state 'CREATE_FAILED', wanted target 'ACTIVE'. last error: 1 error occurred: │ * subnet-04bdeb40bc6cfdc4c, subnet-098f6bd57eea12e52, subnet-062620f94a0f7824c: Ec2SubnetInvalidConfiguration: One or more Amazon EC2 Subnets of [subnet-04bdeb40bc6cfdc4c, subnet-098f6bd57eea12e52, subnet-062620f94a0f7824c] for node group general-devsecops-2023072807281029660000000e does not automatically assign public IP addresses to instances launched into it. If you want your instances to be assigned a public IP address, then you need to enable auto-assign public IP address for the subnet. See IP addressing in VPC guide: https://docs.aws.amazon.com/vpc/latest/userguide/vpc-ip-addressing.html#subnet-public-ip
Khi bạn provisioning 1 eks trên public subnet mà bạn gặp lỗi trên thì quay lại vpc và check đã khai báo config này hay chưa?
# Specify true to indicate that instances launched into the subnet should be assigned a public IP address map_public_ip_on_launch = true
Understanding EKS version upgrades using modules.
Bước đầu tiền thì nó sẽ Upgrade Control Plane lên đầu tiên.
– Module sẽ đi qua các resource là aws_eks_cluster resource và gán vào value của cluster_version.
– AWS upgrades cái control-plane node tại chỗ và trong serial, API sẽ downtime trong 1 vài giây, Nếu trong thời khách đó bạn có nhận được status 5xx hoặc 4xx nếu bạn tranh thủ test thử.
Bước tiếp theo là managed add-ons
Trong module thì, cluster_addons sẽ phụ thuộc cluster. Sau khi control plane report cài new version thì terraform tính toán cái compatible default add-on versions và sẽ deploy theo nó nếu bạn không pin version.
Ở phần Node groups roll forward sẽ chia làm 2 tình huống là EKS Managed và Node groups roll forward
trong quá trình này quá trình rollout Kubernetes evicts pods sẽ sảy ra
Chúng ta sẽ xoáy sâu vào EKS Managed node-group.
Có những trường hợp như sau:
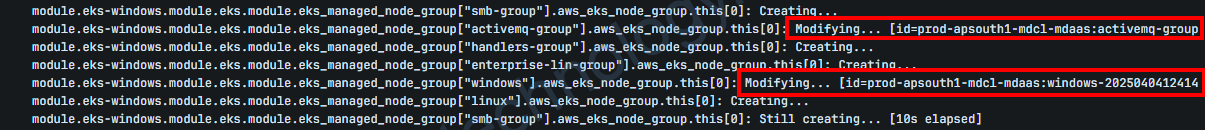
Những trường hợp modifying -> nó edit launch-template lên version mới -> update launch-template version mới trong auto scaling Group.
-> trường hợp này không đang lo ngại.
Những trường hợp Creating… -> thì nó sẽ thực hiện tạo ra 1 cài launch-template mới -> Tiếp đến là Tạo Autoscaling Group mới -> integrate với launch-template mới tạo trước đó.
Ở Case Create thì sẽ nguy hiểm nếu desire trong terraform khác desire đang chạy trên console AWS.
Ví dụ như trong terraform desire đang là 1 nhưng trên console AWS là mười.
Về bản chất, Nó tạo lên ASG mới 1 con node ready thế là nó terminate ASG cũ.
Khiến cho các pod không có đủ node để migrate sang 1 cách đột ngội.
https://github.com/hashicorp/terraform-provider-aws/blob/main/internal/service/eks/node_group.go#L93
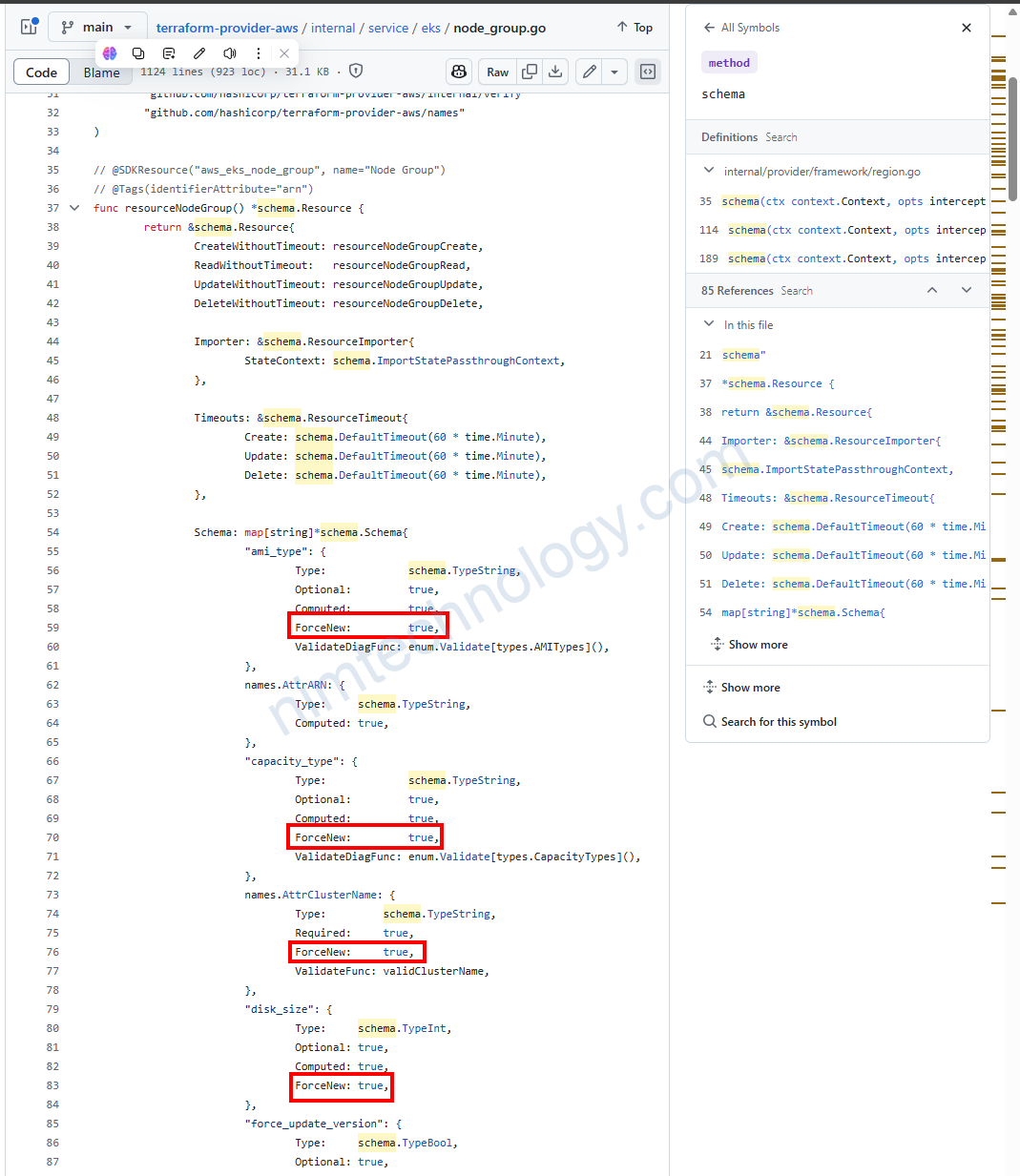
Nếu bạn thay các value như ami_type hoặc instance_type vì nó đang có ForceNew: true
thì terraform sẽ đưa ASG vào trường hợp creating và bạn cần cẩn thận.